TOTPRadius VPN Portal - Security
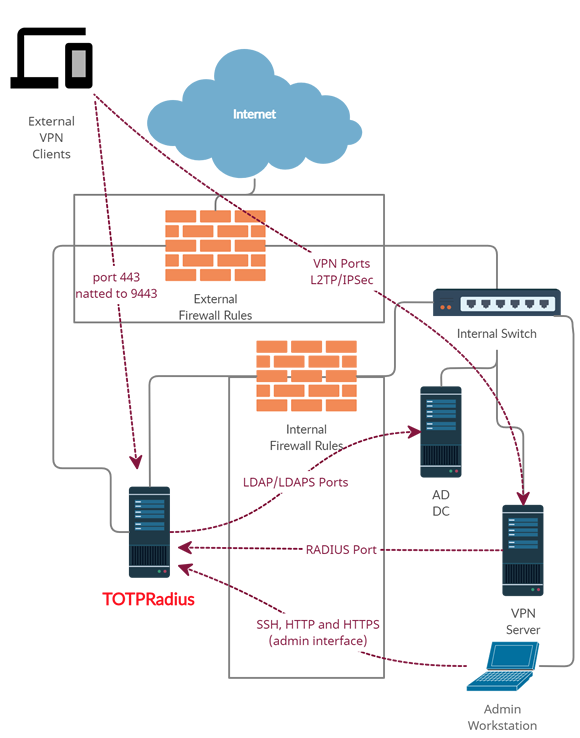
VPN Portal is a subcomponent of TOTPRadius appliance and is required to implement several features, such as LDAP-based self-service enrollment, FIDO2/Passwordless or Azure AD (Microsoft Entra ID) Oauth2/SSO VPN access for your users (available starting from v0.2.5).The principle behind VPN Portal is that it has to be accessible from the public internet, so there is an additional configuration required in your network layout. The web portal is running as a separate web server on the same virtual appliance, instead of standard https port (443) used for admin interface, the VPN web portal responds on port 9443. This port cannot be used directly for technical reasons, so has to be NATted to port 443.
The recommended network layout is displayed below
Approved Security Label
For obvious reasons, this portal has to be exposed to the public network. We understand the potential risks and hesitations of making a web application accessible to the whole planet, therefore to ensure the security of the VPN Portal is at the highest level, we have contracted an independent security company, SySS GmbH , to conduct a full penetration testing against this web application and produce a report.
The team from SySS GmbH has completed the penetration testing and produced a security certificate available below:
The TOTPRadius VPN Portal component is currently labeled as "Certified Website - Approved Security" by SySS Gmbh

About
Installation and configuration
- Installation and initial configuration
- Network configuration
- Migrating from older versions
- LDAP Configuration
- Azure AD Configuration
- Self-service enrollment portal
- Web and LDAPS Certificates
- Syslog configuration
- Single-factor authentication exceptions
- Slave appliance mode
- Dynamic RADIUS Attributes
Integration guides
Blog
04-04-2026
Understanding FIDO User Verification Modes and the always_uv Setting
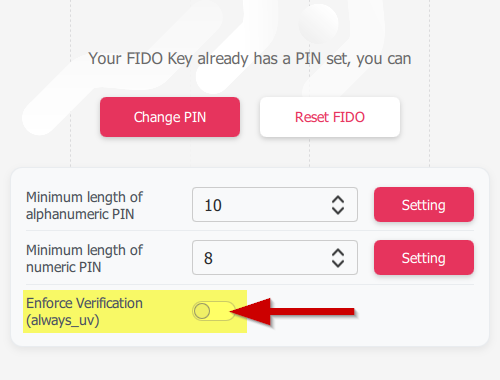 Token2 R3.3 and later FIDO2 keys enforce user verification by default with always_uv = true, improving security, though some platforms and apps like Windows 10, macOS, and certain legacy clients may fail to handle this override correctly.
Token2 R3.3 and later FIDO2 keys enforce user verification by default with always_uv = true, improving security, though some platforms and apps like Windows 10, macOS, and certain legacy clients may fail to handle this override correctly.
05-03-2026
Introducing TOTPVault — self-hosted TOTP management for teams
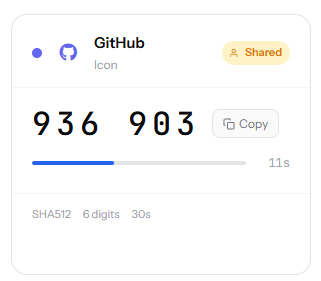 Most TOTP apps work by distributing copies of the secret to every person who needs access — fine for personal accounts, but for shared service accounts it means MFA secrets scattered across people's phones with no clean way to revoke access when someone leaves.
Most TOTP apps work by distributing copies of the secret to every person who needs access — fine for personal accounts, but for shared service accounts it means MFA secrets scattered across people's phones with no clean way to revoke access when someone leaves.
21-12-2025
Android, NFC, and the Missing Piece of WebAuthn
 For years, Android users have faced a frustrating limitation—Android does not support CTAP2 over NFC. This means no PIN verification and no discoverable credentials (passkeys) when using NFC, and therefore limited to simple U2F-style flows without user verification. That said, there finally seems to be a solution.
For years, Android users have faced a frustrating limitation—Android does not support CTAP2 over NFC. This means no PIN verification and no discoverable credentials (passkeys) when using NFC, and therefore limited to simple U2F-style flows without user verification. That said, there finally seems to be a solution.
